Zyxel’s guidance for the recent attacks on the ZyWALL devices
Summary
Zyxel recently became aware of a cyberattack targeting our ZyWALL devices. These vulnerabilities already have patches - we took immediate action as soon as we become aware of them, and have released patches, as well as security advisories for CVE-2023-28771, CVE-2023-33009, and CVE-2023-33010.
Simultaneously, Zyxel has been urging users to install the patches through multiple channels, including issuing several security advisory newsletters to registered users and advisory subscribers; notifying users to upgrade via the Web GUI’s push notification for on-premises devices; and enforcing scheduled firmware upgrades for cloud-based devices that haven’t yet done so.
What are the vulnerabilities?
Improper error message handling in some firewall versions could allow an unauthenticated attacker to execute some OS commands remotely by sending crafted packets to an affected device.
A buffer overflow vulnerability in the notification function in some firewall versions could allow an unauthenticated attacker to cause denial of service (DoS) conditi ons and even a remote code execution on an affected device.
A buffer overflow vulnerability in the ID processing function in some firewall versions could allow an unauthenticated attacker to cause DoS conditions and even a remote code execution on an affected device.
What are the symptoms?
- Device becomes unresponsive
- Unable to reach device’s Web GUI or SSH management interface
- Network interruptions
- VPN connections disconnecting
What products and firmware versions are affected?
| Affected series | Affected versions for CVE-2023-28771 |
Affected versions for CVE-2023-33009 |
Affected versions for CVE-2023-33010 |
Latest firmware |
|---|---|---|---|---|
| ATP | ZLD V4.60 to V5.35 | ZLD V4.60 to V5.36 Patch 1 | ZLD V4.32 to V5.36 Patch 1 | ZLD V5.36 Patch 2 |
| USG FLEX | ZLD V4.60 to V5.35 | ZLD V4.60 to V5.36 Patch 1 | ZLD V4.50 to V5.36 Patch 1 | ZLD V5.36 Patch 2 |
| USG FLEX50(W) / USG20(W)-VPN | N/A | ZLD V4.60 to V5.36 Patch 1 | ZLD V4.25 to V5.36 Patch 1 | ZLD V5.36 Patch 2 |
| VPN | ZLD V4.60 to V5.35 | ZLD V4.60 to V5.36 Patch 1 | ZLD V4.30 to V5.36 Patch 1 | ZLD V5.36 Patch 2 |
| ZyWALL/USG | ZLD V4.60 to V4.73 | ZLD V4.60 to V4.73 Patch 1 | ZLD V4.25 to V4.73 Patch 1 | ZLD V4.73 Patch 2 |
What should you do and how can the risk be mitigated?
Zyxel strongly recommends that our users install the latest firmware to patch the mentioned CVEs for optimal protection. Additionally, we advise our users to follow the guidance below for temporary mitigation and precautionary purposes:
- Unless it is absolutely necessary for you to manage devices from the WAN side, disable HTTP/HTTPS services from WAN.
- If you still need to manage devices from the WAN side:
- Enable Policy Control and add rules to only allow access from trusted source IP addresses; and
- Enable GeoIP filtering to only allow access from trusted locations.
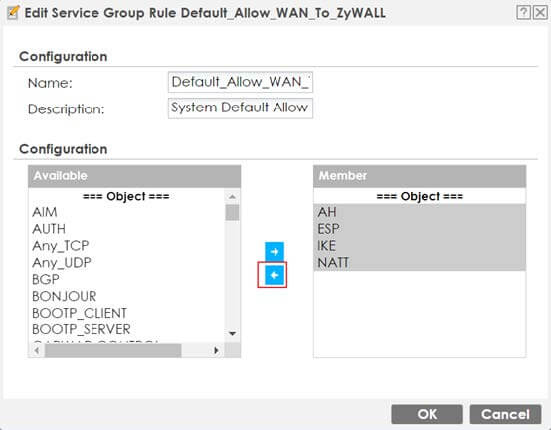
- If you don’t need to use the IPSec VPN function, disable the UDP Port 500 and Port 4500 as shown below.
If you have any further questions or concerns about your network security, please reach out to Zyxel’s support team for assistance. Our security professionals are happy to provide guidance or customized recommendations based on your specific environment.
