Network Perimeters Need Extra Layers of Protection
New workplace flexibilities has given us the ability to connect, share, and collaborate from anywhere. Now there are more roaming users connected to branch offices and cloud apps. Securing your business is no longer only about securing the network.
Workplace
80%
Workers use SaaS apps at work without approval from IT department*1Workforce
82%
Mobile workers do not use VPN for Internet access when working*2Applications
85%
Increase in business SaaS apps by 2025*3Detect More Attacks, Protect More Roaming Users
As networks are becoming more decentralized, apps and data are served from multiple resources on-premises along with public cloud services. While having access to all these off-network activities and all these services online, the boundaries are much more difficult to define and consequently defend from attacks.
See VideoBorderless Perimeter Security with Astra
Astra service secure your remote users that are roaming everywhere outside existing perimeter. It puts all aspects of security protection back into the hands of the network administrator and allows them to monitor and secure users regardless of their locations.
Ability to identify people, device, and applications for authentication and access control
Real-time web-browsing detection for what is being identified as malicious
Timely actions to various levels of threats by determined policies
Features of Astra Portal and App
| Features | Portal | App |
|---|---|---|
| Status Monitoring | *4 | |
| Overview & Analysis for All Members | ||
| Content Filter Policy | ||
| Website/IP Block Monitoring | *4 | |
| Website/IP Block Monitoring for All Members | ||
| Website/IP Block Alert | *4 | |
| Website/IP Block Alert for All Members | ||
| Member Management | ||
| Device Management |
Manage Endpoints from One Place
Astra portal is a unified platform to help your IT administrators to easily manage employees' devices. Astra coordinates and prioritizes alert, reports, analysis of abnormal events, provide instant visibility and control with customized security requirements such as policy settings and blocking websites before any data breaches.
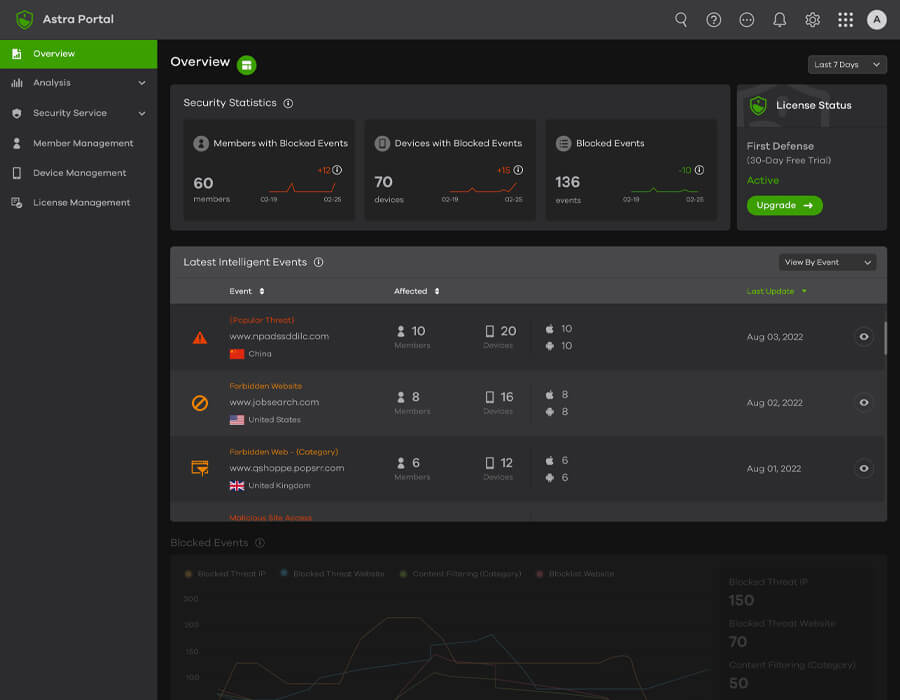
Intelligence-led Security
See the latest abnormal activities viewed by event or member. Predict and identify which of these suspicious events qualify as malicious attacks. Investigate a threat analysis by going through its detailed graph of real-time web-browsing detection comparing to last 7 day or 24 hours.
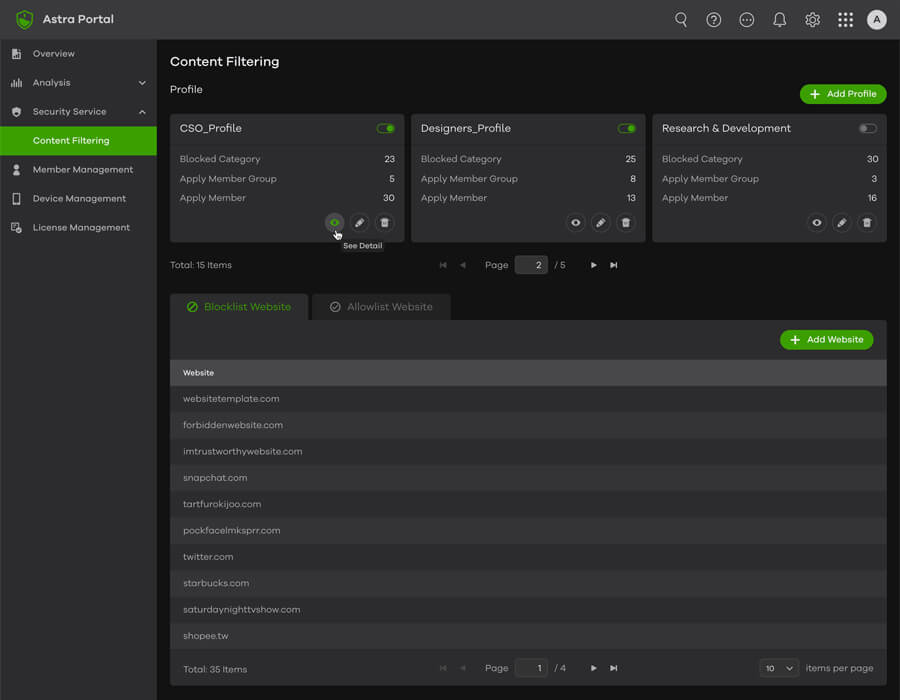
Custom Content Filtering Block Access
Prevent threats by configuring content filtering profile, adding profile with restricted content categories for different members. Add forbidden website URLs into blacklisted or whitelisted groups that members are not allow to access based on your business needs.
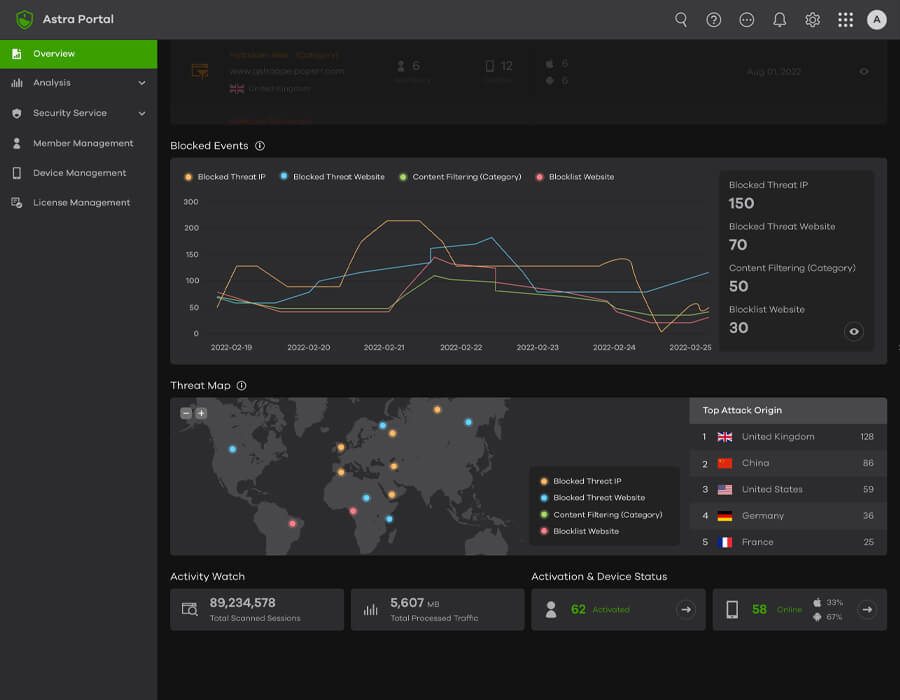
Threat Statistics
View popular threats, blocked web URLs, malicious sites and IP address to help distinguish what is being identified as malicious through activities and threat map. Track event details and gives visibility into past events of the blocked reasons, owner, and online/offline status.
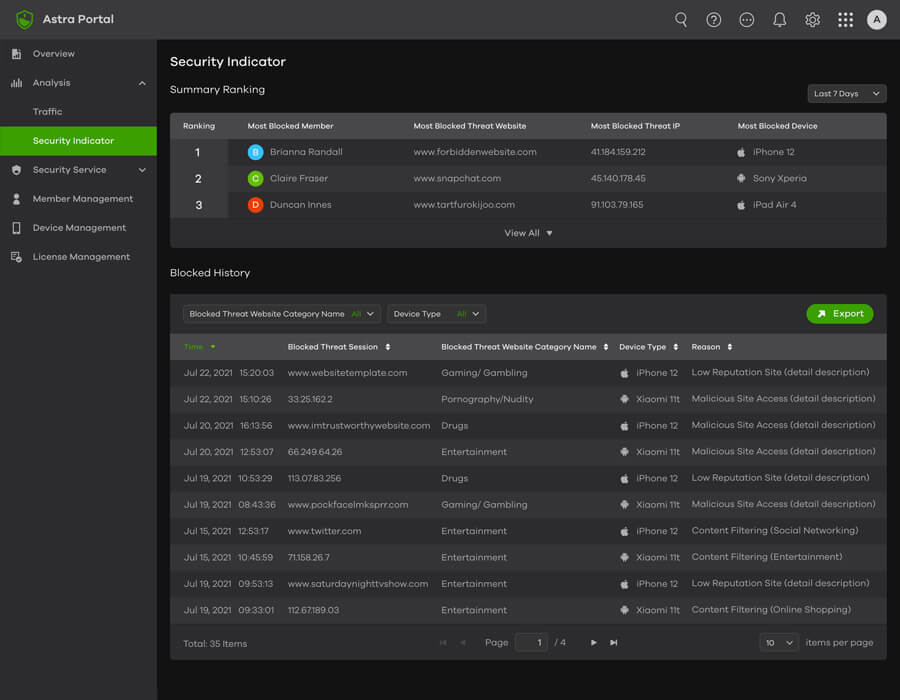
Network Traffic Analysis and Security Indicator
Timely traffic monitoring and 7-day historical data storage for admin, warning you with app notification and email alerts when a traffic event matches your rule criteria. Summary ranking for most blocked member, blocked website/IP, and blocked device to allow you monitor the members more effectivity.
Easy to Setup and Use with Astra App
Protect you and your employees from phishing and exploit attacks, by enhancing your endpoint security with engineless Astra. You can also control and manage the mobile device’s safety without sacrificing performance. Get ahead of malicious threats anytime and anywhere with Astra app.
Keep remote users secure
with Zyxel Astra
Share your feedback
with us
Learn how to access and
use Zyxel Astra Portal
- *1 Techopedia - Janalta Interactive Inc: Intro to Cloud Security: 5 Types of Risk
- *2 TheBestVPN.com: VPN statistics and usage
- *3 Gartner: Gartner says cloud will be the centerpiece of new digital experiences
- *4 The features are only available for member role

