不被妥協和完整的網路防護
得獎紀錄Zyxel ZyWALL ATP系列是專用於中小型企業的高級威脅防護防火牆,由智慧雲網路保護提供支援,特別是在應對未知威脅方面。該系列不僅支援所有Zyxel安全服務,如Web過濾、智能應用程式、安全管理、惡意程式阻擋,信譽過濾器等,還支援沙箱和SecuReporter。還包括一個資訊圖表儀錶板,可提供高性能並確保作為自我發展的解決方案提供全面的保護。
線上Demo通過雲端使ATP更加提升
為了增強網路安全性,我們讓ATP防火牆與雲端Nebula結合以強化資安防護功能,通過協作網路防禦和沙箱配置讓您高枕無憂。借助我們不斷發展的安全保護,獲取詳細的調查報告、主動監控、網路活動的高可見性。

全面的威脅檢測和預防
ATP防火牆配備沙箱等多種保護工具,可阻止未知惡意軟件和zero-day威脅,CDR可以在網路邊緣阻止或隔離受感染的客戶端,遏制威脅並防止進一步損害。它簡化了對您所有業務網路的保護,無需擔心。

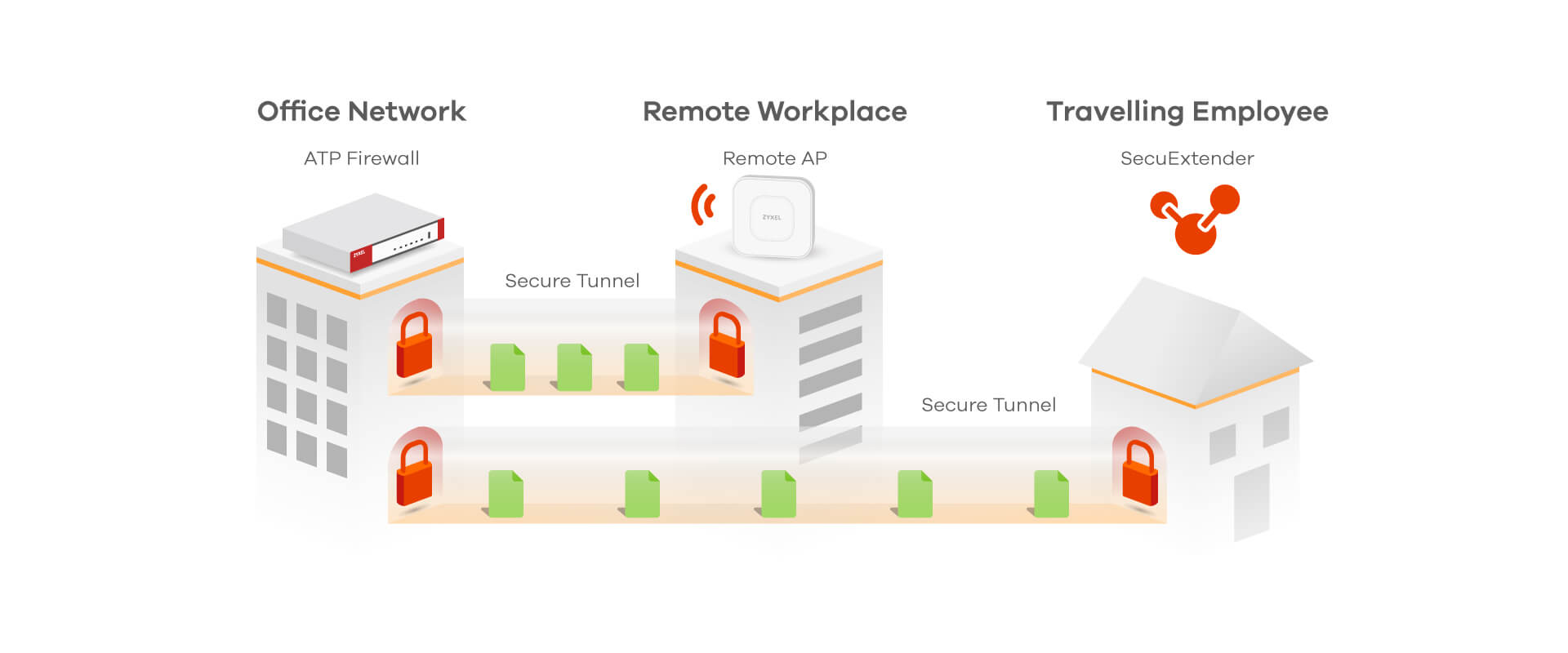
異地辦公就像在公司裡一樣安全
我們提供各種不同遠端訪問選項的產品,包括用於總部與分公司之間的防火牆、具有 Secure WiFi 的 遠端無線基地台 ,和異地辦公的VPN軟體管理,讓端點設備防護更加延伸。
提高可視性以優化資源使用
ATP 可以幫助企業管理員工正在使用的應用程式,並快速一目了然地查看所有應用程式。超過3700種應用被分類為不同的標籤。只需選取即可阻止或取消阻止。對於應用程式監視和管理來說,就是這麼簡單。

Just Connect with Nebula
經銷商、託管服務供應商 (MSP) 和網路管理員可透過 Zyxel 的Nebula單一雲端網路管理平台, 能夠體現其簡易、可擴展性、靈活性、並且能降低 IT 風險和成本的特色。
Nebula提供強大,輕鬆且可擴展的網路連接,它們能協同運作來消除與不同品牌設備連網之間經常產生的複雜性和安全風險。
透過我們的Nebula集中雲端管理平台,能夠連接、保護和管理資安防火牆、交換器、無線基地台和LTE/5G路由器。
Zyxel不斷增長的產品組合為客戶提供超過 80 種支援Nebula設備,其透過 NebulaFlex以優異的方式引入新產品和現有產品。從部署家庭辦公室到分佈式網路配置,Zyxel的Nebula產品組合可以符合客戶現在和未來所有型態的預算、功能和可擴展性。